To explain in detail, in order to implement a live Data Connection from SAP Analytics Cloud to SAP HANA using a Direct Connection, you must configure your on-premise SAP HANA system to support SSO for live data connections that use the direct connection type.
In this short video, you will see how to this. First, we will configure our SAP HANA XS engine for HTTPS connection using a specified Web Dispatch User specially created for that matter and then we’ll see how to configure CORS support on your SAP HANA system.
Prerequisites
- If end users will access the live data connection from outside of your corporate network, ensure that the SAP Information Access (InA) service (/sap/bc/ina/service/v2) on your SAP HANA server is exposed to browser users, either directly, or via a reverse-proxy.
- Ensure that the InA package (/sap/bc/ina/service/v2) or a higher-level package is configured for SAML authentication using the same identity provider URL as your SAP Analytics Cloud tenant. For details, see the SAP HANA XS documentation.
- Ensure the sap.bc.ina.service.v2.userRole::INA_USER role is assigned to all users who will use the live connection and ensure those users are SAML configured. This role is required in addition to the usual roles and authorizations that are granted to users for data access purposes.
- If your SAP HANA server is exposed to internet users via a reverse proxy, in your SAML identity provider configuration, ensure that the Assertion Consumer Service (ACS) endpoint URL for the SAP HANA service provider is set to the SAP HANA server’s reverse proxy URL. For example, https://<reverse-proxy-host>/sap/hana/xs/saml/login.xscfunc.
All the following steps are to ensure that your SAP HANA XS server is configured for HTTPS (SSL) with a signed certificate, and that you know which port it is using for HTTPS requests. For details, see Maintaining HTTP Access to SAP HANA and SAP Knowledge Base Article 2502174. The next lines are directly extracted from that knowledge base.
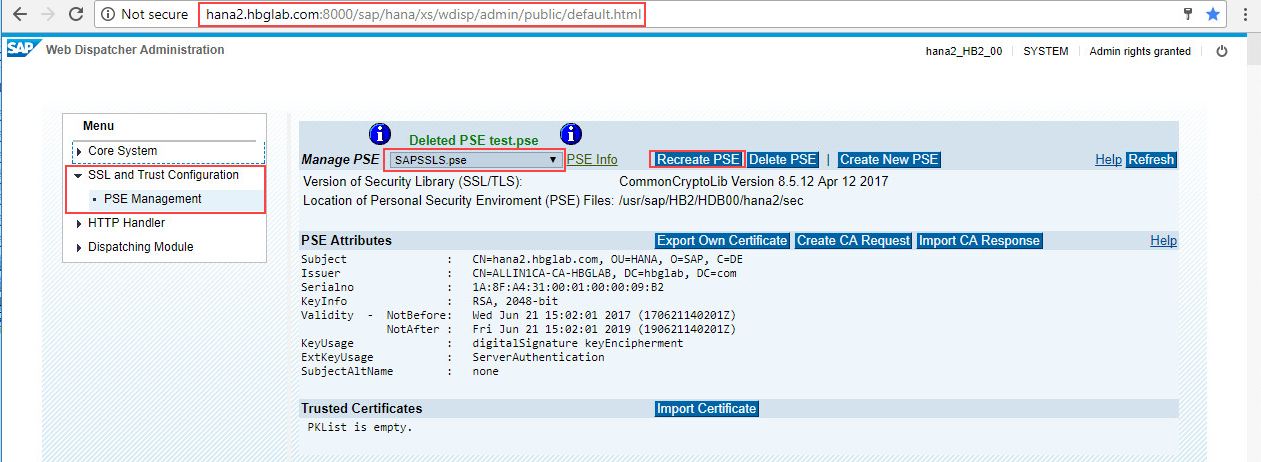
- Open the Website of the Web Dispatcher Administration (http://<yourhanaserver>:<yourhttpport>/sap/hana/xs/wdisp/admin/public/default.html)
IMPORTANT: The user needs the role “WebDispatcherAdmin” - Switch to the Tab of SSL and Trust Configuration -> PSE Management
- Choose the SAPSSLS.pse and click “Recreate PSE”
- In the Distinguished Name field add a new key/value pair such as DNS=”shortname”. You can add multiple SANs by separating them by colon. This will transform these values into the Subject Alternative Name.
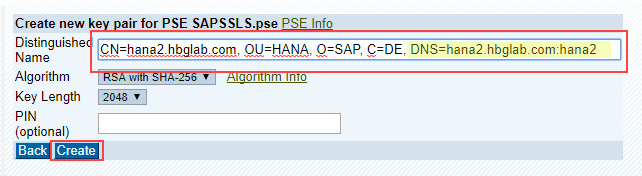
- After clicking Create you will see a new overview of the certificate request.
IMPORTANT: You won’t see the SubjectAltName filled at this stage. - Click “Create CA Request”.

- Select the full text and copy it to the clipboard.
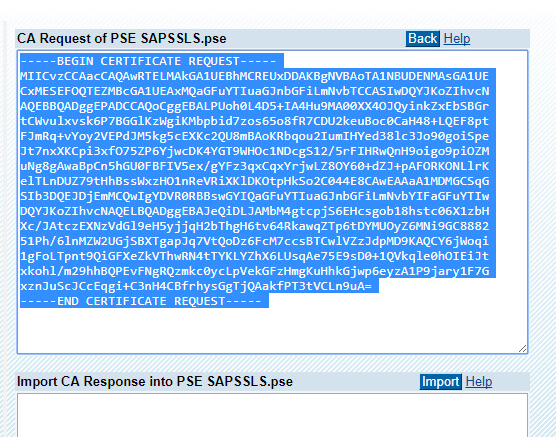
- OPTIONAL: Check CSR:
https://www.sslshopper.com/csr-decoder.html - Sign the request (using Windows CA Server as sample)
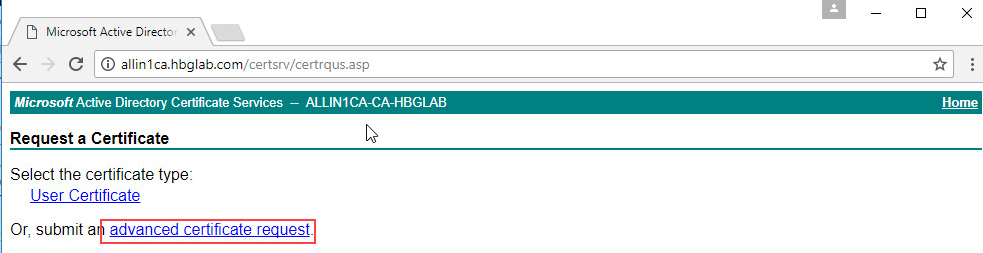
- Open the Certificate Services website of your CA Server (http://CASERVER/certsrv/) to “Request a certificate”
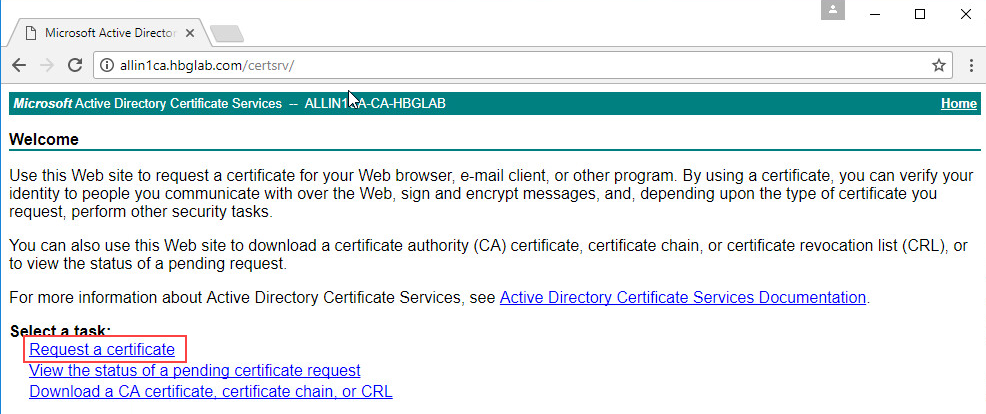
- Click on “advanced certificate request”
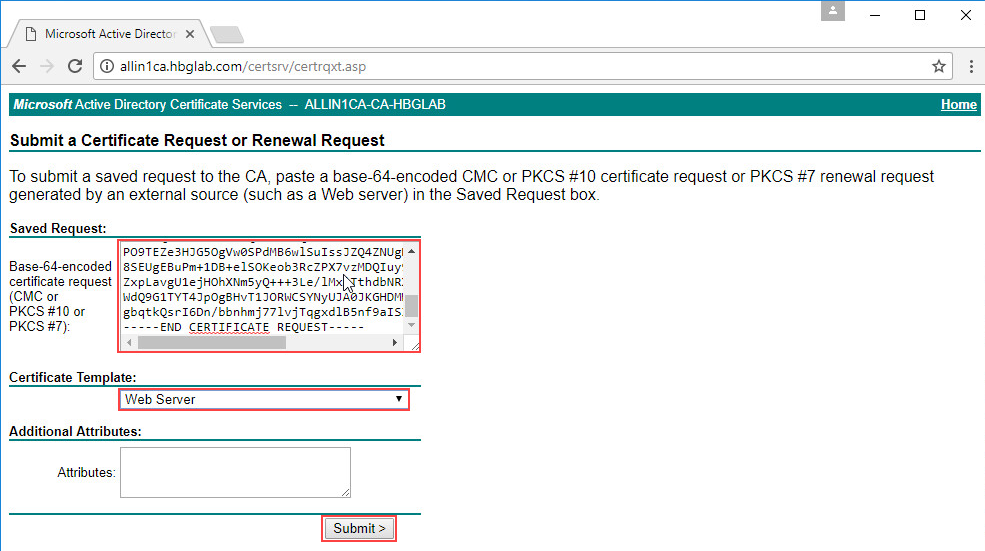
- Paste the previous copied content into the “Saved Request” window. As Certificate Template choose “Web Server”. If you do not have this Template in the list contact your CA Administrator please. Submit the request.
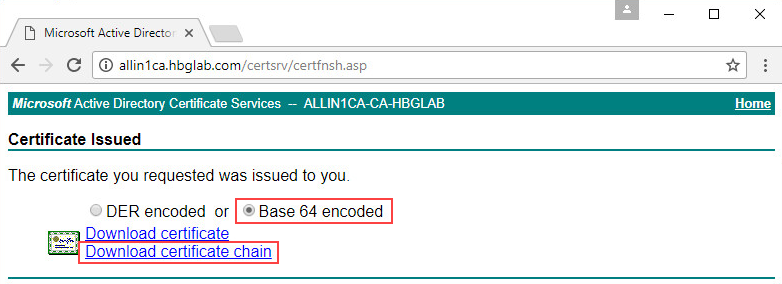
- Base 64 encoded has to be used then download the full certificate chain as .p7b file
- Open the Certificate Services website of your CA Server (http://CASERVER/certsrv/) to “Request a certificate”
- Implement the signed certificate
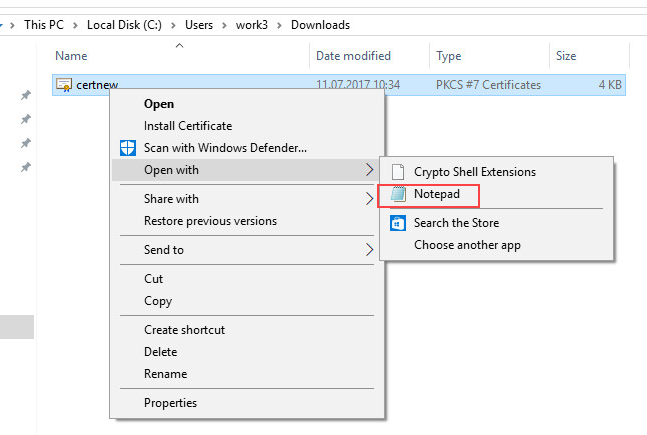
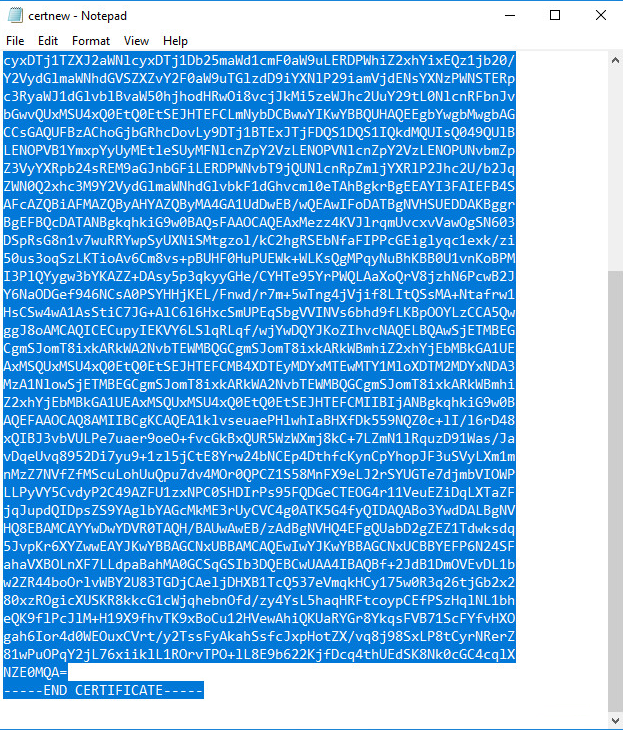
- Open the saved .p7b with notepad or any other editor
- Select the full text and copy it to the clipboard.
- Go back to the Web Dispatcher Administration site and paste in the copied content into the “CA Response” field, then click Import
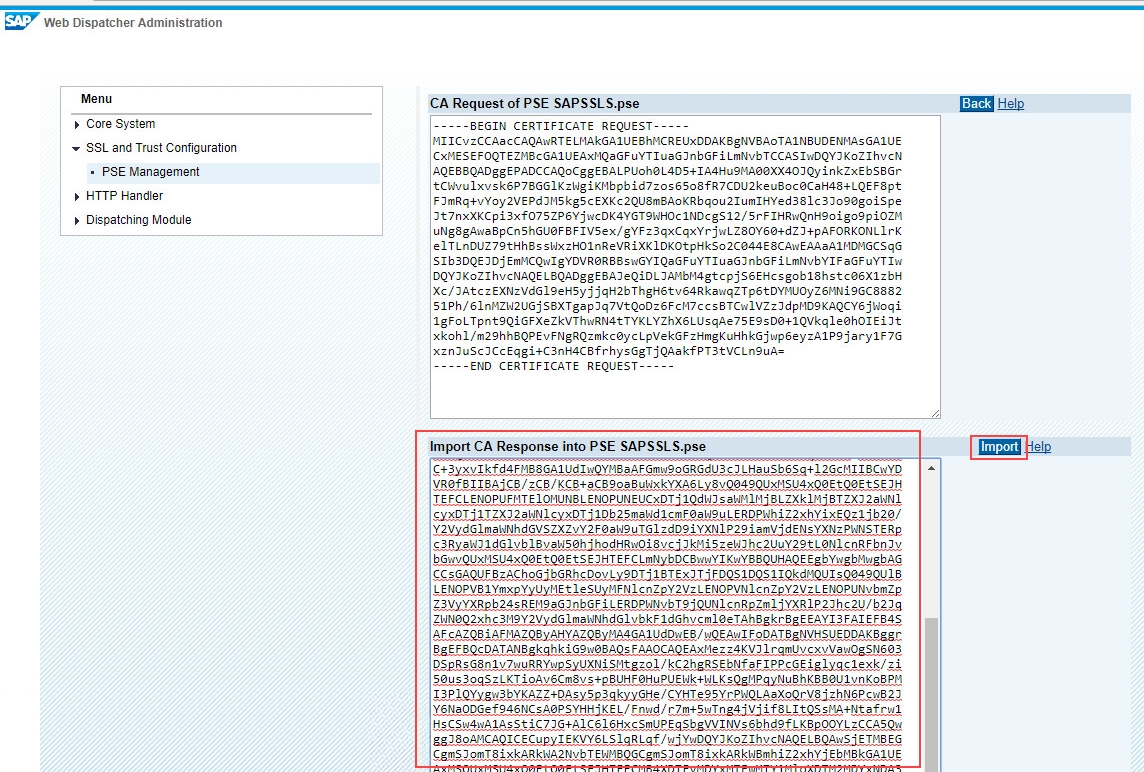
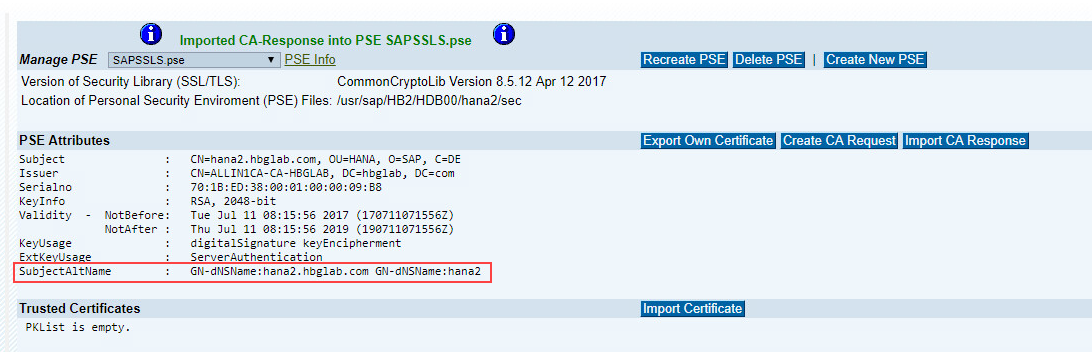
- After the import you will see the Subject Alternative Name field is now filled.
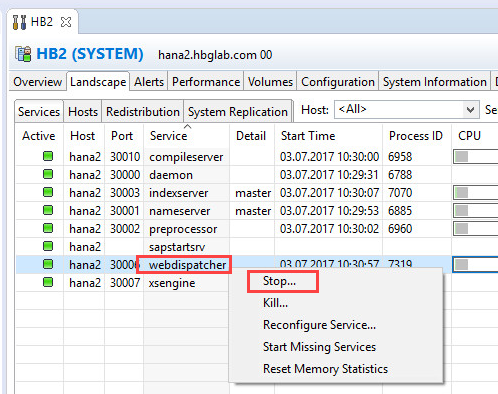
- After importing the Certificate the “webdispatcher” has to be restarted. This can be done in HANA Studio by just stopping it. It should be restarted automatically.
- Open the saved .p7b with notepad or any other editor
Now that we have set up our SAP HANA XS server for HTTPS (SSL) with a signed certificate, we simply need to Configure CORS support on your SAP HANA system.
You must ensure that the HTTP responses from the InA service to users’ web browsers include CORS headers.
- Enable CORS support for the InA package directly on the SAP HANA system:
- Log on to SAP HANA Studio as the System user or with other admin/developer credentials.
- Switch to the SAP HANA Development perspective and in the Repositories panel, navigate to sap.bc.ina.service.v2.
- Open the .xsaccess file and replace its contents with the following text, ensuring that the allowOrigin value matches the host of your SAP Analytics Cloud tenant:
{ "exposed" : true, "prevent_xsrf" : true, "authentication": [ { "method" : "Basic" }], "rewrite_rules": [ { "source": "(GetResponse|Perspectives|GetVersion|GetServerInfo|Analytics|Metadata|Planning).*", "target": "ina_v2.xscfunc?service=$0" } ], "authorization" : [ "sap.bc.ina.service.v2::Execute" ], "cors": { "enabled": true, "allowMethods": ["GET","POST","HEAD","OPTIONS"], "allowOrigin": ["https://<customer-prefix>.<data-center>.sapbusinessobjects.cloud"], "maxAge": 3600, "allowHeaders": ["x-csrf-token","accept","authorization","x-request-with","content-type","x-sap-cid"], "exposeHeaders":["x-csrf-token","accept","authorization","x-request-with","content-type","x-sap-cid"] }, "cache_control" : "no-cache, no-store", "headers": { "enabled": true, "customHeaders": [ {"name":"Access-Control-Allow-Credentials","value":"true"} ] } }NoteThe allowOrigin variable should match your SAP Analytics Cloud tenant URL.
- Save your changes and activate the file.
Congratulations, you are done, you can now go to SAP Analytics Cloud and configure your Direct Connection to SAP HANA.
